Documentation
Features
- Multi-App Configuration
- App Icons
- App Themes
- PWA Configuration
- Composable Pages
- Documentation Project
- Authentication
- Authorization
UI & Experience
Page Blocks
Authorization
This document exposes how resources are protected in NextKit.
Role Based Access Control
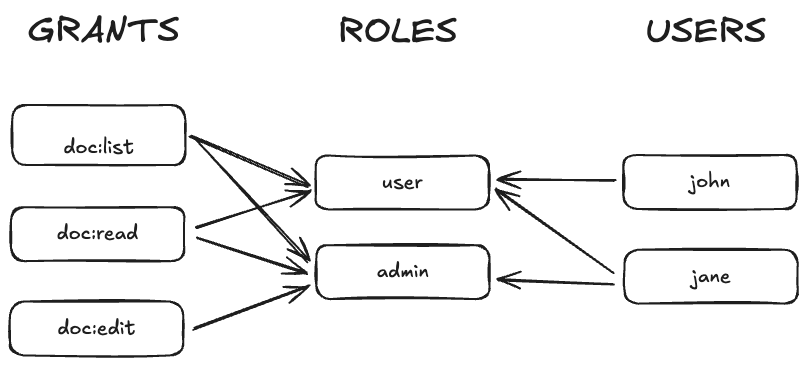
NextKit's RBAC is composed by:
- grants: Is a single ACL entity that can be required to perform an action
- roles: Is a group of grants, roles are assigned to users for a specific AppID
- users: Is an actor in the system, and can assume any given role.
Example:
Editing a document requires the
doc:editgrant.
Janehas the role ofadminand that role is associated withdoc:edittherefore JANE CAN perform the action.
Johnhas the role ofuserand that role is NOT associated withdoc:edittherefore JOHN CAN NOT perform the action.
RBAC is App Specific
Grants and roles are global entities, they are just names and can be reused by many different Apps. An "admin" is a role that makes sense for a TodoApp and a Notebook app anyway.
But the association of grant -> role and user -> role is App specific.
It means that what an "admin" can do must be defined for each App. Also what is John's role must be re-defined for each App.
Evaluate a Policy
const result = evaluatePolicy({ requireFlag: "api/foo", requireRole: "admin", requireGrants: ["doc:write", "doc:read"], // require all requireAnyGrant: ["doc:write", "doc:read"], // stop at first match });